In this article, I’ll walk through the exact steps I used to set it up on AWS using OpenVPN Access Server.
Who This Guide Is For
This guide is intended for:
- Beginners to intermediate users who want to build a personal VPN
- Readers with basic AWS and EC2 knowledge (no deep networking required)
- Anyone looking for a simple OpenVPN setup using the AWS Marketplace, rather than installing and configuring OpenVPN manually
If you’re comfortable launching an EC2 instance and following step-by-step instructions, this guide should be easy to follow.
What You’ll Need
- An AWS account with access to EC2
- OpenVPN Access Server from the AWS Marketplace
- Basic familiarity with Amazon EC2 (launching instances, security groups)
- A computer running Windows, macOS, or Linux
- Around 20–30 minutes to complete the setup
💡 Note: OpenVPN Access Server includes 2 free simultaneous VPN connections, which is sufficient for personal use.
Step 1: Launch OpenVPN from the AWS Marketplace
 |
| (Figure 1) |
- After selecting the OpenVPN Access Server AMI in EC2, choose t2.small (or another instance type that fits your needs) under Instance Type.
- Review all other settings (VPC, subnet, storage, security groups) and click Launch.
- When prompted, create a new key pair or select an existing one, then download the
.pemfile—this is required to connect to your instance via SSH.
- Once the instance is running, connect using SSH with the following command (replace with your actual file name and public IP of the EC2 instance):
ssh -i “name_pem_file.pem” openvpnas@ec2-ipaddress.ap-south-1.compute.amazonaws.com (login)
Once you SSH into your OpenVPN Access Server instance, you’ll see the OpenVPN Access Server End User License Agreement (EULA) in the terminal.
- Carefully read through the license terms.
- To proceed, type: yes
- After accepting the EULA with
yes, the setup wizard will ask a few configuration questions. - For all prompts (network settings, interface selection, etc.), press Enter to accept the default values. When you reach the prompt:
Should client traffic be routed by default through the VPN? [no]: Typeyesand press Enter. - When prompted for the OpenVPN Admin password, enter a secure password of your choice. This will be the password for the
openvpnadmin user. - The setup will complete using default settings, and the server will be ready for first-time login.
Once done, you’ll get the URL for the admin web interface, typically: https://<ec2-public-ip>:943/admin and the end-user portal: https://<ec2-public-ip>:943/
You’ll likely see a security warning because the SSL certificate is self-signed. Proceed anyway (add an exception in your browser).
 |
| Admin web interface |
Step 2: Log In as Admin and User
- Username:
openvpn - Password: The one you set during setup
- Click Sign In
Step 3: Download the VPN Client
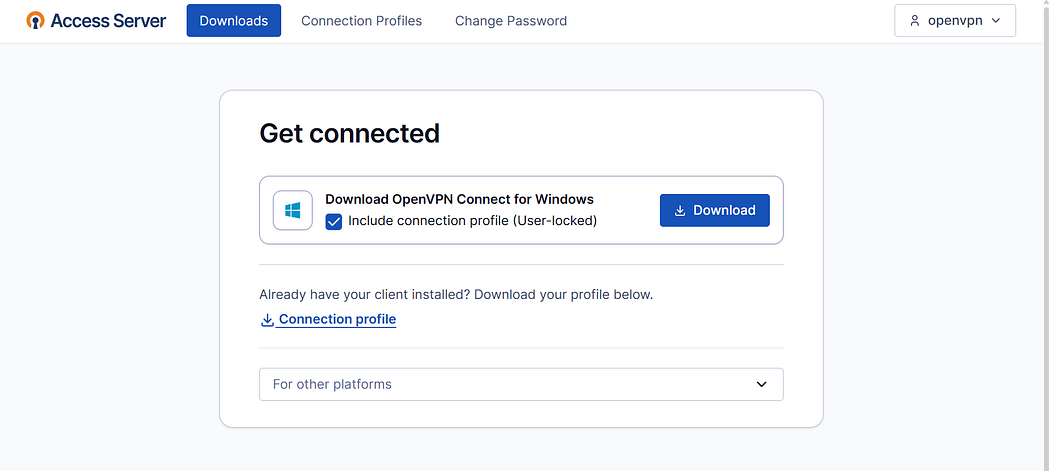
- Once logged in, you’ll see a dashboard with a “ Download” section.
- Select the appropriate OpenVPN client for your operating system (Windows, macOS, Linux, iOS, Android).
- Download and install the client on your device.You should see a screen like this (Figure 2)
Step 4: Get User Configuration
- After installing the client, go back to the portal.
- Click “Yourself → Download Profile” or “Connect”, depending on the portal version.
- This downloads a .ovpn configuration file or automatically configures the client.
Step 5: Connect to VPN
- Open the OpenVPN client and import the
.ovpnprofile if needed. - Connect using your username and password.
- Once connected, your device is now routed through the VPN.
Comparison: Before and After connecting to VPN
OpenVPN on AWS is a simple and effective way to secure your network and enable remote access. By launching the Access Server, configuring routing, and managing users, you can create a full-featured VPN quickly. Leveraging AWS ensures reliability, scalability, and ease of management. With this setup, you now have a secure, flexible solution for connecting users safely from anywhere.
Disclaimer:
This content is provided solely for educational and informational purposes and outlines a general approach to configuring OpenVPN on AWS. Actual configurations, security controls, and compliance requirements may differ based on individual environments. Users are solely responsible for ensuring lawful, authorized, and secure use of the information provided. This guide must not be used for any illegal, unauthorized, or malicious purposes. The author and publisher disclaim all liability for any direct or indirect damages, data loss, or security incidents arising from the use or misuse of this content.




Comments
Post a Comment